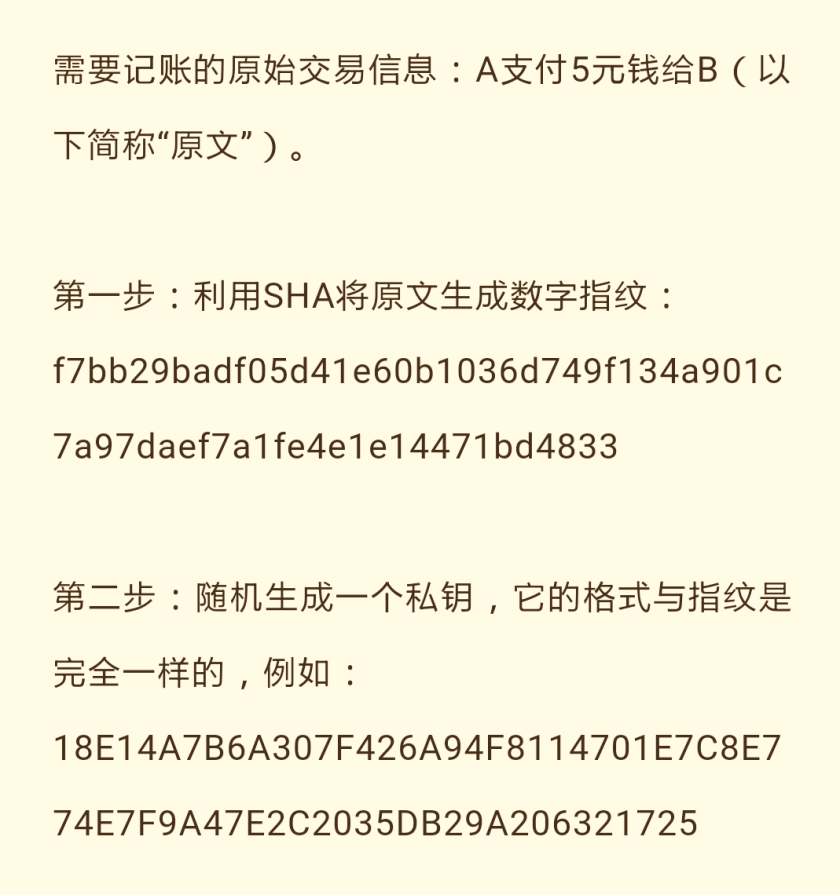
Encryption & Decryption: ECC (Elliptic Curve Cryptography):

Sending End: Encryption
1) SHA algorithm generates “Digital Signature” ;
2) Generate random “Private Key”.
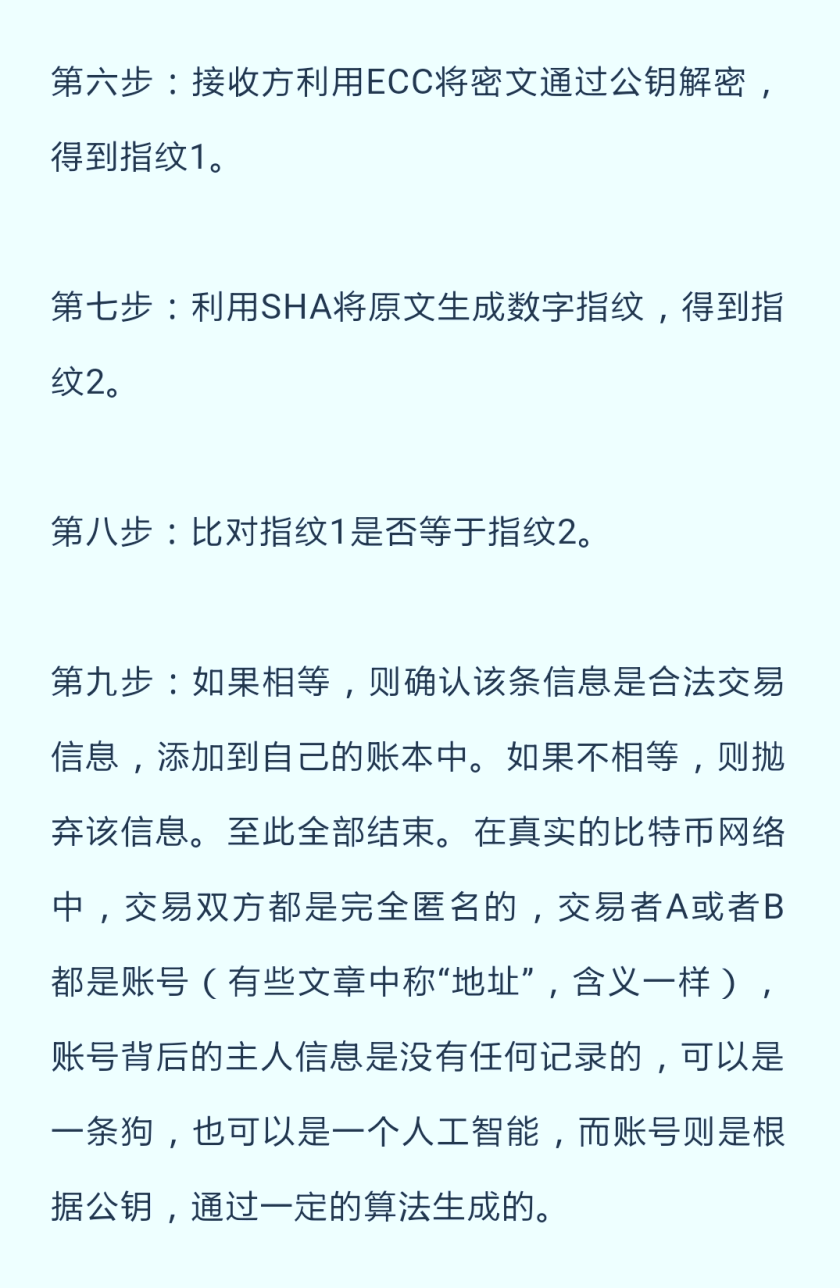
第3-6步骤:
3) ECC encrypts the text with “Private Key”;
4) From the Private Key generates a “Public Key”;
5) Send out the “original message” and the “Public Key” with the “encrypted message” from 3);

Receiving End: Decryption
6) ECC with Public Key generates Digital Signature 1 (S1);
7) Use SHA algorithm on the original message generates Digital Signature 2 (S2);
8) If S1 = S2, then accept transaction, otherwise reject.

One thought on “Blockchains and Application in Bitcoins”